Proofpoint: Leading the Charge in Digital Security
- TronsIT Solutions
- 0 Comments
In today’s evolving cybersecurity landscape, companies face increasing cyber threats, from phishing and ransomware to insider attacks and data breaches. As agencies shift to remote work, cloud-based totally applications, and AI-driven automation, the need for strong cybersecurity solutions has never been more. Proofpoint protection consciousness has emerged as a vital component in defending organizations against cyber threats by focusing on employee training, proactive threat detection, and AI-powered security solutions.
According to a 2025 Gartner cybersecurity report, 90% of protection breaches are caused by human error, emphasizing the need for security awareness training. Proofpoint provides organizations with the tools to educate employees, detect potential threats, and strengthen organization security infrastructure, ensuring organizations stay protected in the age of digital transformation.
The Growing Cybersecurity Threat Landscape
Cybercriminals are constantly evolving their tactics to exploit vulnerabilities in enterprise networks. In 2025, the global cost of cybercrime is expected to reach $10.5 trillion annually, making cybersecurity a top priority for businesses worldwide. The most common security threats include:
- Phishing attacks: Cybercriminals use misleading emails to steal sensitive information such as login credentials and financial info.
- Ransomware: Malicious software encrypts business data, demanding payment for its launch.
- Insider Threats: Employees with access to essential data may deliberately or accidentally compromise security.
- Business Email Compromise (BEC): Hackers impersonate executives or employees to trick organizations into transferring funds or sharing confidential information.
Proofpoint’s security awareness programs help organizations identify, mitigate, and prevent these threats by training employees to recognize suspicious activities and respond appropriately.
Why Security Awareness Training is Crucial
A 2025 Cybersecurity Workforce Study found that 68% of employees lack fundamental cybersecurity knowledge, increasing the risk of data breaches and financial losses. Proofpoint’s security awareness training educates employees on how to:
- Identify and report phishing emails and social engineering tactics.
- Use multi-factor authentication (MFA) and strong passwords.
- Recognize insider threats and data leaks.
- Follow compliance regulations such as GDPR, HIPAA, and ISO 27001.
Cybersecurity Awareness Training Effectiveness
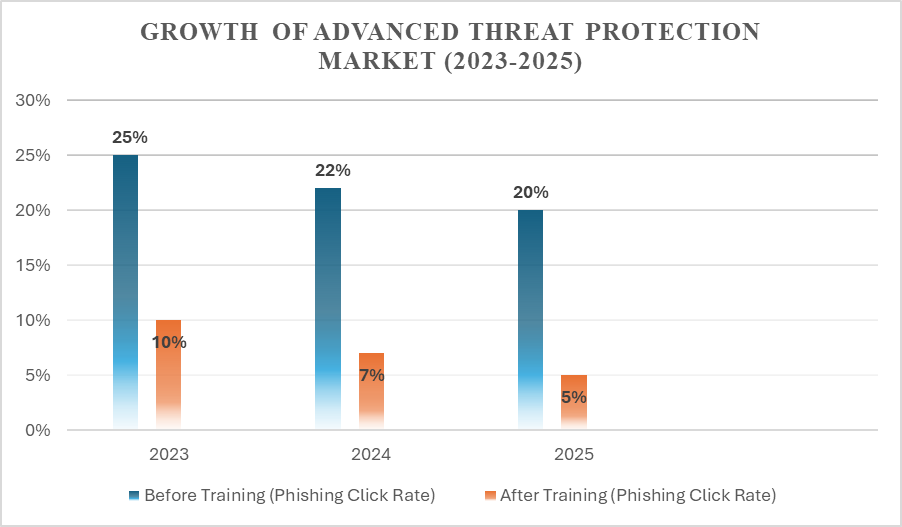
The data demonstrates that ongoing security training significantly reduces the likelihood of employees falling victim to phishing attacks, ultimately improving organizational security.
Cybersecurity Best Practices for Employees
Organizations must implement cybersecurity best practices for employees to further strengthen enterprise security. These include:
1. Implementing Strong Password Policies
Employees should use complex passwords and enable multi-factor authentication (MFA) for all work-related accounts. Password managers can help employees securely store and manage credentials.
2. Recognizing and Reporting Suspicious Emails
Phishing attacks remain the most common entry point for cybercriminals. Employees must:
- Verify the sender’s email address before clicking on links or downloading attachments.
- Report suspicious emails to IT security teams immediately.
3. Secure Use of Public Wi-Fi and Remote Work Tools
With hybrid work models becoming the norm, employees should avoid using public Wi-Fi networks to access sensitive company data. Businesses should enforce the use of Virtual Private Networks (VPNs) and endpoint security solutions to protect remote workers.
4. Updating Software and Security Patches Regularly
Cybercriminals often exploit outdated software with known vulnerabilities. Employees and IT teams must ensure that:
- Operating systems and applications are updated regularly.
- Security patches are applied promptly to prevent cyberattacks.
5. Preventing Insider Threats
Organizations should establish role-based access control (RBAC) to restrict access to critical data and monitor employee activities for suspicious behavior.
Organizations can significantly reduce security risks and enhance overall network protection by integrating these best cybersecurity practices into daily workflows.

The Role of Advanced Threat Protection Solutions
With cyber threats becoming more sophisticated, businesses need next-generation cybersecurity tools beyond traditional antivirus and firewalls. Advanced threat protection solutions provide:
- AI-Powered Threat Detection: Machine learning algorithms analyze real-time data to detect anomalous behavior and suspicious activities.
- Email Security & Phishing Protection: Proofpoint’s solutions block phishing attempts, prevent malware infections, and stop email fraud attacks before they reach employees.
- Endpoint Protection & Cloud Security: Ensures that all devices, servers, and cloud applications are protected from cyber threats.
- Incident Response Automation: AI-driven security systems can automatically contain threats and neutralize attacks, reducing response times and minimizing damage.
Adopting advanced threat protection solutions is projected to grow rapidly by 2025 as businesses prioritize cyber resilience and proactive security strategies.
In Conclusion
As cyber threats evolve, businesses must proactively approach cybersecurity by implementing comprehensive security awareness programs, best practices for employees, and advanced threat protection solutions.
At TronsIT Solutions, we specialize in advanced cybersecurity solutions that help businesses secure their digital infrastructure, train employees, and protect against advanced cyber threats. Whether you need Proofpoint security awareness training, compliance management, or AI-powered security solutions, TronsIT Solutions ensures your organization stays one step ahead of cybercriminals. Contact us today to strengthen your cyber defense strategy!
Related Posts
Proofpoint: Leading the Charge in Digital Security
- TronsIT Solutions
- April 7, 2025
In today’s evolving cybersecurity landscape, companies face increasing cyber threats, fro ..
Think Before You Discard: How Improper Data Disposal Can Lead to Breaches
- TronsIT Solutions
- April 30, 2025
In the world of cybersecurity, people often think of threats in terms of firewalls, ransomware, ..



